 Check Point Endpoint Security - Secure Access
Check Point Endpoint Security - Secure Access
A guide to uninstall Check Point Endpoint Security - Secure Access from your system
You can find on this page detailed information on how to uninstall Check Point Endpoint Security - Secure Access for Windows. It is made by Check Point Software Technologies Ltd.. Open here for more info on Check Point Software Technologies Ltd.. The application is often placed in the C:\Program Files (x86)\Checkpoint\Endpoint Security directory (same installation drive as Windows). Check Point Endpoint Security - Secure Access's entire uninstall command line is C:\Program Files (x86)\Checkpoint\Endpoint Security\Uninstaller.exe {9923056D-94D0-485A-9556-EA73F490952C}. The program's main executable file is named iclient.exe and occupies 1,005.50 KB (1029632 bytes).Check Point Endpoint Security - Secure Access installs the following the executables on your PC, taking about 6.29 MB (6596138 bytes) on disk.
- CPESDbg.exe (41.54 KB)
- cpmsi_tool.exe (129.39 KB)
- fwlogctl.exe (21.65 KB)
- iclient.exe (1,005.50 KB)
- installUtil.exe (76.00 KB)
- PiReg.exe (33.39 KB)
- sc_wnt2k.exe (16.08 KB)
- Uninstaller.exe (61.00 KB)
- zlscvins.exe (59.50 KB)
- command_line.exe (61.52 KB)
- cpmsi_tool.exe (129.52 KB)
- openmail.exe (49.51 KB)
- TracCAPI.exe (585.52 KB)
- TracSrvWrapper.exe (3.39 MB)
- TrGUI.exe (613.51 KB)
- vna_install64.exe (14.91 KB)
- vna_utils.exe (69.51 KB)
This page is about Check Point Endpoint Security - Secure Access version 7.6.306.001 only. Click on the links below for other Check Point Endpoint Security - Secure Access versions:
How to uninstall Check Point Endpoint Security - Secure Access using Advanced Uninstaller PRO
Check Point Endpoint Security - Secure Access is an application offered by the software company Check Point Software Technologies Ltd.. Frequently, users try to uninstall this program. Sometimes this can be troublesome because performing this manually requires some experience regarding Windows program uninstallation. The best QUICK practice to uninstall Check Point Endpoint Security - Secure Access is to use Advanced Uninstaller PRO. Here is how to do this:1. If you don't have Advanced Uninstaller PRO already installed on your Windows PC, add it. This is good because Advanced Uninstaller PRO is the best uninstaller and general tool to clean your Windows system.
DOWNLOAD NOW
- go to Download Link
- download the program by clicking on the DOWNLOAD NOW button
- install Advanced Uninstaller PRO
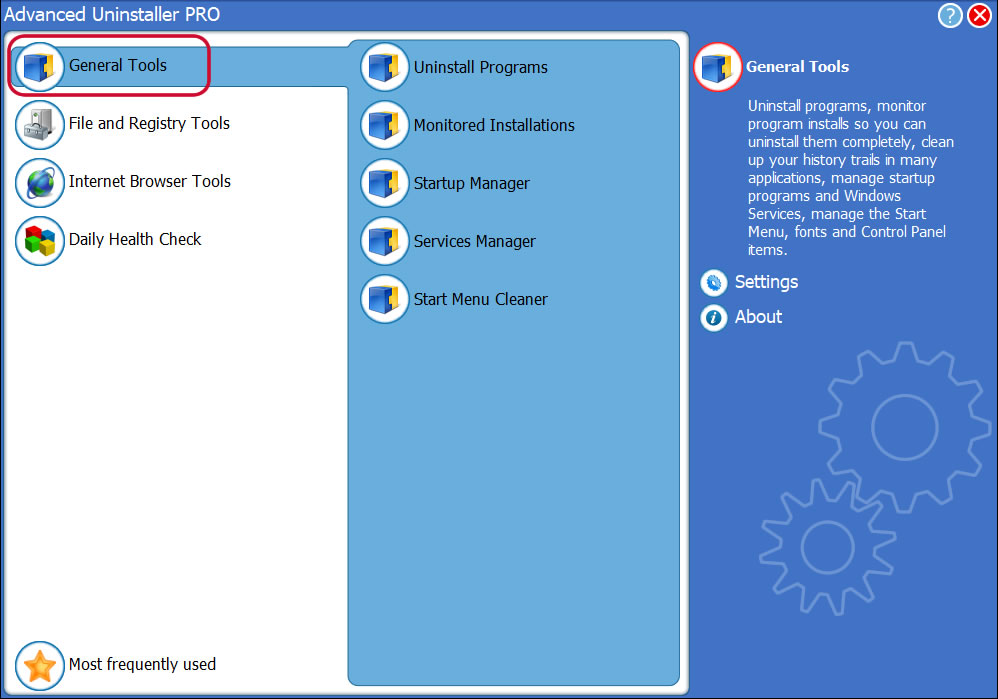
3. Press the General Tools category
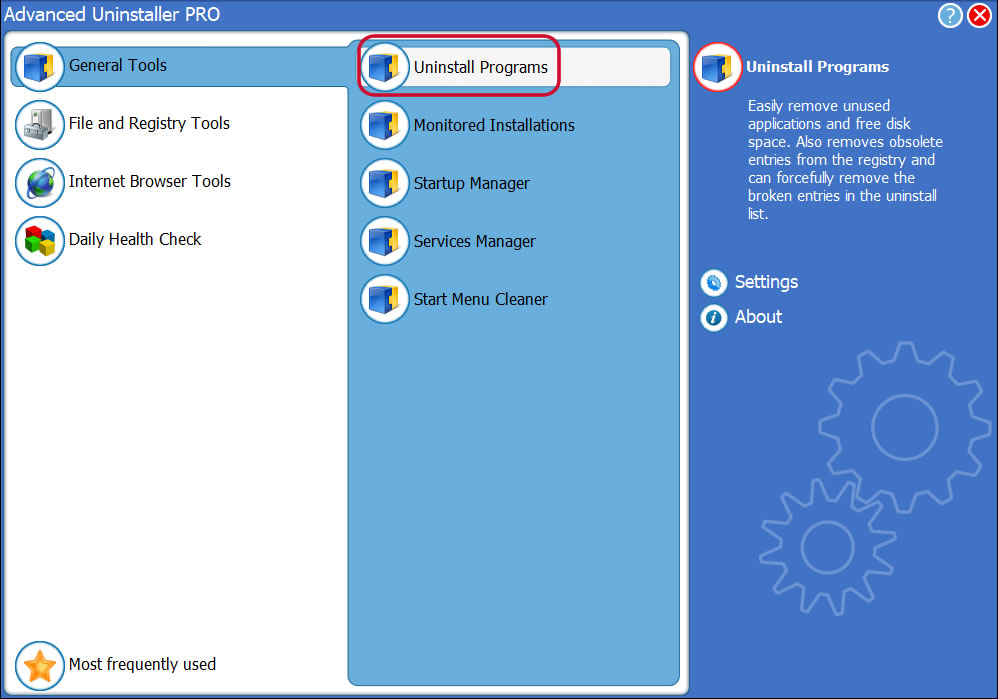
4. Click on the Uninstall Programs button
5. All the programs existing on your PC will appear
6. Navigate the list of programs until you find Check Point Endpoint Security - Secure Access or simply activate the Search feature and type in "Check Point Endpoint Security - Secure Access". The Check Point Endpoint Security - Secure Access program will be found automatically. When you click Check Point Endpoint Security - Secure Access in the list of programs, some data regarding the program is made available to you:
- Star rating (in the lower left corner). This explains the opinion other users have regarding Check Point Endpoint Security - Secure Access, from "Highly recommended" to "Very dangerous".
- Reviews by other users - Press the Read reviews button.
- Technical information regarding the application you are about to uninstall, by clicking on the Properties button.
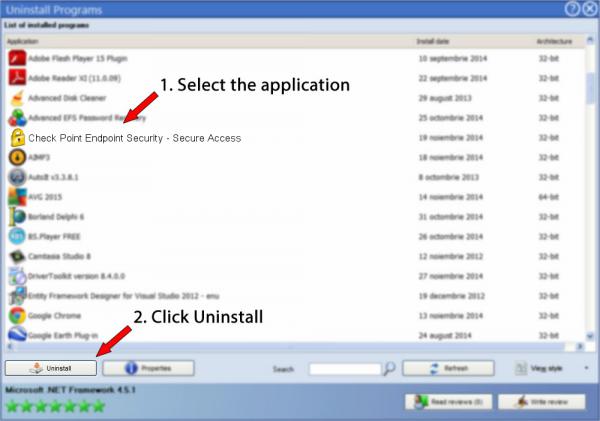
8. After uninstalling Check Point Endpoint Security - Secure Access, Advanced Uninstaller PRO will offer to run an additional cleanup. Press Next to perform the cleanup. All the items of Check Point Endpoint Security - Secure Access which have been left behind will be found and you will be asked if you want to delete them. By removing Check Point Endpoint Security - Secure Access with Advanced Uninstaller PRO, you can be sure that no Windows registry entries, files or directories are left behind on your disk.
Your Windows computer will remain clean, speedy and able to take on new tasks.
Disclaimer
The text above is not a piece of advice to uninstall Check Point Endpoint Security - Secure Access by Check Point Software Technologies Ltd. from your computer, we are not saying that Check Point Endpoint Security - Secure Access by Check Point Software Technologies Ltd. is not a good application for your PC. This text simply contains detailed info on how to uninstall Check Point Endpoint Security - Secure Access in case you decide this is what you want to do. Here you can find registry and disk entries that other software left behind and Advanced Uninstaller PRO discovered and classified as "leftovers" on other users' computers.
2017-03-02 / Written by Dan Armano for Advanced Uninstaller PRO
follow @danarmLast update on: 2017-03-02 20:27:33.090